How Do Phone Lockers Improve Data Security and Compliance?
Phone lockers improve data security by establishing a physical "air gap" between sensitive environments and mobile devices, effectively eliminating the risk of unauthorized audio/video recording and data exfiltration. By centralizing mobile storage, organizations can satisfy strict physical access control requirements mandated by regulatory frameworks like HIPAA, ISO 27001, and GDPR.
Key Security Controls Provided:
- Elimination of unauthorized recording (audio/video/photo) in restricted zones.
- Prevention of "Shadow IT" and unauthorized network tethering via personal hotspots.
- Mitigation of insider threats by controlling data egress points.
- Verification of audit readiness for physical security compliance standards.
The Modern Threat Landscape: Why Physical Barriers Matter in a Digital World
In a modern security framework, every mobile device is a potential endpoint vulnerability. While cybersecurity software protects the network, it cannot stop a high-resolution camera from capturing proprietary designs on a monitor or a microphone from recording a sensitive board meeting.
The shift from viewing phone lockers as a mere tool for "distraction-free" environments to a critical "risk-free" security control is driven by the evolution of mobile hardware. Today’s devices feature AI-powered audio enhancement and 5G capabilities that can bypass traditional corporate firewalls through tethering. Physical isolation is often the only definitive way to secure a "Data-Free Zone."
Common Mistakes to Avoid:
- Relying solely on "honor system" policies without physical enforcement.
- Underestimating the range of modern mobile microphones in sensitive meeting areas.
3 Ways Phone Lockers Directly Improve Data Security

Eliminating Unauthorized Recording and Espionage
Mobile devices are the primary tools for modern industrial espionage. A single photo of a prototype or a leaked audio recording of a strategic pivot can result in millions of dollars in lost intellectual property. By requiring cell phone lockers at the entrance of R&D labs or executive suites, you ensure that no unauthorized recording hardware enters the room.
Preventing "Shadow IT" and Unauthorized Tethering
One of the most overlooked security risks is the personal hotspot. Employees can connect corporate laptops to their phone’s 5G network, bypassing all corporate traffic monitoring, malware filtering, and data loss prevention (DLP) tools. Lockers ensure that these "rogue access points" are kept outside the security perimeter.
Mitigating the Insider Threat
Most data breaches involve an internal element. Physical control over devices prevents the quick "snap-and-send" of sensitive data. It adds a layer of friction that deters opportunistic data theft and ensures that any data leaving the facility must pass through digital checkpoints, not a pocketed smartphone.
Mapping Phone Lockers to Global Compliance Standards
For many industries, physical device security is not just a best practice—it is a requirement for certification.
- HIPAA (Healthcare): Physical safeguards (Standard 164.310) require entities to limit physical access to electronic information systems. Lockers provide a verifiable method to keep personal recording devices away from screens displaying Protected Health Information (PHI).
- ISO 27001: Control A.11.1 focuses on defining security perimeters. Implementing a locker policy for "Secure Areas" demonstrates a commitment to physical access control during a certification audit.
- GDPR: Article 32 requires "technical and organizational measures" to ensure a level of security appropriate to the risk. For processors of high-risk data, physical storage is a primary organizational measure.
Example: During a SOC 2 audit, showing a documented employee phone storage policy paired with physical locker logs can serve as evidence of operational security.
Industry-Specific Use Cases for Secure Storage
Healthcare & HIPAA Compliance
In clinics and hospitals, phone lockers prevent staff or visitors from inadvertently capturing patient data in the background of photos or videos, significantly reducing the risk of a HIPAA violation.
Government & Defense (SCIF Requirements)
Sensitive Compartmented Information Facilities (SCIFs) have long mandated that all personal electronics be stored in external lockers. This "Electronic-Free Zone" is the gold standard for preventing signal intelligence leaks.
Corporate R&D and Financial Services
In environments where "first-to-market" is everything, or on trading floors where communication is strictly regulated, lockers ensure that sensitive data remains within the intended digital ecosystem.
Common Mistake: Ignoring the "convenience factor." High-security facilities often see higher compliance rates when they provide lockers with built-in charging ports, incentivizing employees to store their devices willingly.
Implementing a "Security-First" Phone Policy
A successful rollout requires more than just hardware; it requires a clear policy.
- Define the Perimeter: Identify which rooms or zones are "Device-Free."
- Select the Right Hardware: Choose lockers with high-grade materials (such as 1.0mm galvanized steel) to prevent tampering.
- Establish Protocol: Will lockers be assigned to individuals, or use guest-style digital codes?
- Communicate the "Why": Focus on protecting both corporate data and employee hardware.
In educational settings, these same principles apply to academic integrity. For more on this, see how phone lockers help during exams and testing.
Frequently Asked Questions
Yes, they serve as a physical safeguard to protect patient privacy. By preventing recording devices from entering areas where PHI is visible, they help organizations meet the "Physical Safeguards" requirement of the HIPAA Security Rule.
Generally, yes, especially in high-security, healthcare, or safety-sensitive environments. Employers have the right to restrict personal device use on company property to protect trade secrets and ensure data security.
Phones are banned because they contain multiple data egress tools, including cameras, microphones, and cellular transmitters. These can be used for espionage, unauthorized data transmission, or bypassing secure networks.
No, they are a physical control designed to stop physical data theft and unauthorized recording. They must be used in conjunction with robust cybersecurity software for total protection.
An insider threat refers to an individual within an organization using their access to harm data security. Mobile devices make this easier by allowing someone to quickly photograph or record sensitive information and transmit it instantly.
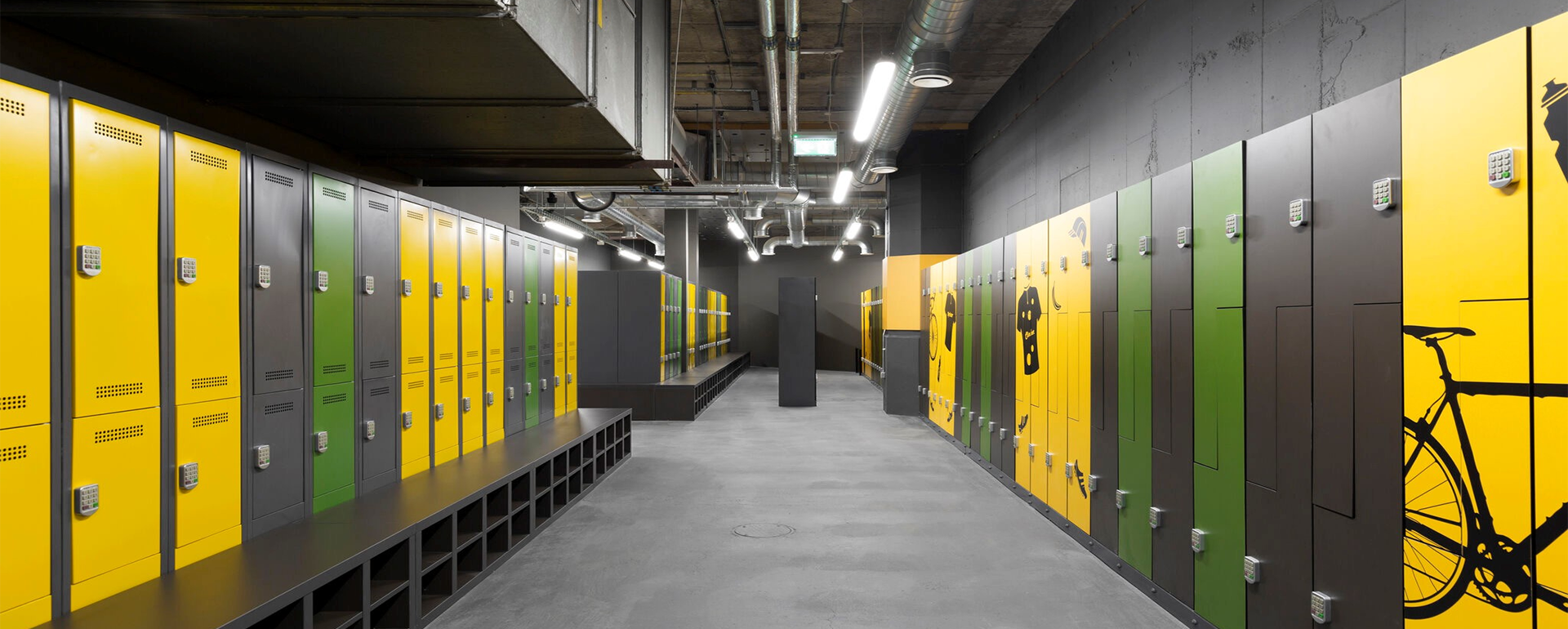
Yes, while the primary goal in these settings is theft prevention rather than data security, the hardware remains similar. You can explore the best gym phone storage solutions for more information on member-facing options.
Conclusion
As digital threats become more sophisticated, the value of a physical barrier cannot be overstated. Phone lockers are no longer just about reducing workplace distractions; they are a vital component of a modern IT security and compliance strategy. By implementing secure storage, you protect your intellectual property, satisfy regulatory auditors, and mitigate the ever-present risk of the insider threat.